Digital Sovereignty Through Control
Data and AI sovereignty plus governance and crisis resilience, measurable in daily operations.
What is Digital Sovereignty?
Sovereignty is control over data flows, access, and decisions.
Standard is Germany or Europe.
When innovation requires a model outside Europe, a controlled exception applies with data classification, data masking, DLP, approval, and review.
Standard vs. Controlled Exception
Standard (Default)
- Hosting in Germany/EU
- Services in Germany/EU
- Open Standards
- Free LLMs with governance
Controlled Exception
- Only defined data classes
- Data masking required
- DLP rules enforced
- Documented approval + review cycle
Minimum Criteria for Digital Sovereignty
Hosting in Germany/EU
All systems and data are hosted in Germany or the EU.
Control over storage
Only you decide where your data resides and for how long.
Control over data flows
Transparent and documented data flows with no unexpected outflows.
Control over access
Who accesses your data? When? Why? Everything is traceable.
Services in Germany/EU
All software services and platforms run in Germany/EU.
Open Source
Preferred: open source code, transparent licenses, no black boxes.
Free LLMs
Large Language Models with open source code enable local deployment and auditability.
Exit option
You can always take your data with you, no vendor lock-in.
What You Get
Data Classification + AI Prompt Rules
Clear structure for what is and isn't allowed.
AI Use Case Approval
Documented approvals for every application.
Exit Plan
How you can exit anytime, without data loss.
Escalation Matrix
Who gets notified when something goes wrong?
Audit Structure
How you can prove compliance anytime.
Frequently Asked Questions
Digital Sovereignty Check in 20 Minutes
Let's discuss your digital sovereignty: practical, measurable, and immediately actionable.
Related Services
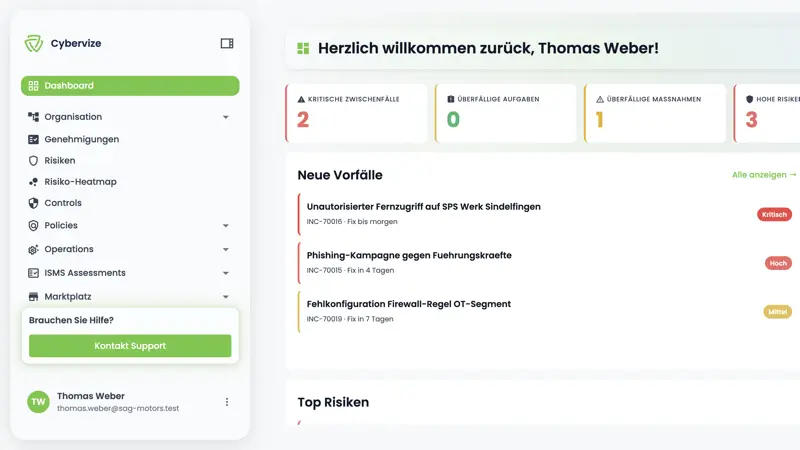
Virtual CISO (vCISO)
Outsourced CISO (vCISO): strategic security leadership at C-level, flexible and cost-effective.
Learn moreInterim CISO
Immediate security expertise for transition phases and critical projects.
Learn moreCybersecurity Assessment
Comprehensive analysis of your IT security posture with actionable roadmap.
Learn more